
Established in 1997, Penta Security’s researchers and developers have had years of experience under their belts, and have been acknowledged for their developments. Hence, our security products are consequently acknowledged by market research firms worldwide.
Each of our web and data security products creates a safe environment for you where you can simply rest assure knowing that the security of your information is in good hands. Please feel free to download brochures on our resources page, or take a look at the overviews of our products below.
Web Security, WAPPLES is an award-winning WAF that accurately detects and prevents web attacks. Without posing hindrances to the system’s quality or speed, it performs functions such as real-time monitoring and prevention of site attacks, forgery/defacing of websites, and data leaks.
Market share leader for three consecutive years, WAPPLES is the Web Application Firewall (WAF) of choice for customers in the Asia Pacific.
Besides blocking basic web attacks, WAPPLES is deployed to effectively guard against sensitive data leakage, block malicious web access and prevent website defacement in this era of intensified attacks.
Powered by an intelligent detection engine, WAPPLES is capable of combating the newest threats, including attacks often utilized in Advanced Persistent Threats (APT) launched by malicious agents to obtain data assets of governments and enterprises or for terrorism or political gains.
Most recently mentioned on the Gartner Asia/Pacific Context: ‘Magic Quadrant for Web Application Firewalls’ 2018
Intelligence Allows Top Performance
While traditional WAFs depend on high-maintenance signature updates for low-accuracy pattern-matching, WAPPLES uses a logic-based detection engine called COCEP™ (Contents Classification and Evaluation Processing).
Utilizing 34 pre-configured detection rules, modified and even unknown attacks are categorized and blocked heuristically and semantically. This proprietary technology allows WAPPLES to deliver superior security with industry-leading accuracy and low false positive rates under various network environments. Maintaining high stability and performance, WAPPLES’ ease of deployment and low operational workload was recognized by Gartner as what made the WAF a popular choice for surveyed clients.
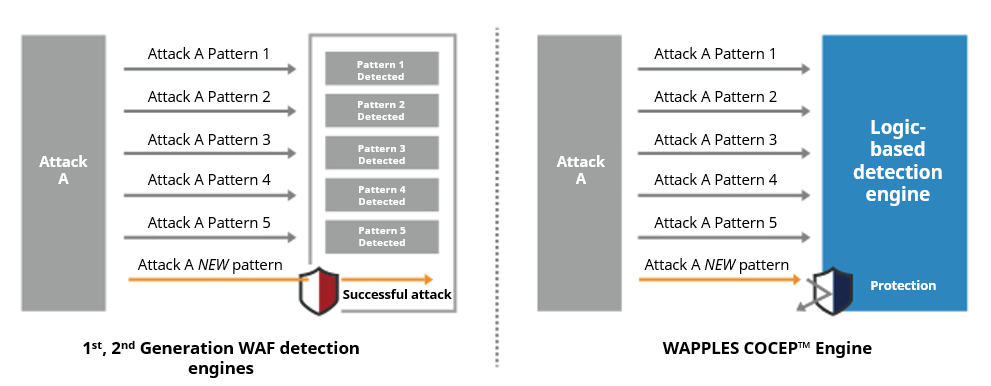
Through the analysis of an attack’s characteristics, WAPPLES is able to identify attacks that utilize new patterns of exploit that often bypass typical WAFs utilizing signature-based detection engines.
1st and 2nd generation WAFs that operate on blacklists and whitelists lag behind due to their reliance on signature updates to detect the latest threats. In comparison, the sophistication of security that WAPPLES can provide greatly surpasses that of signature-based WAFs.
Features
High-Accuracy Web Attack Defense |
Easy to Install & Configure |
|
|
Supports Various Environments |
High Performance and Stability |
|
|
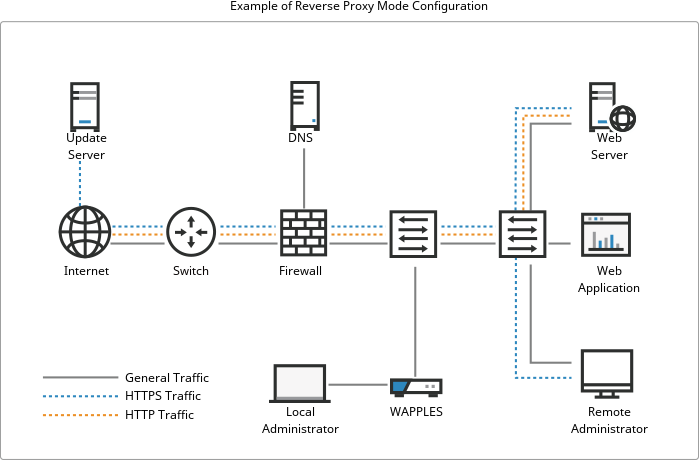
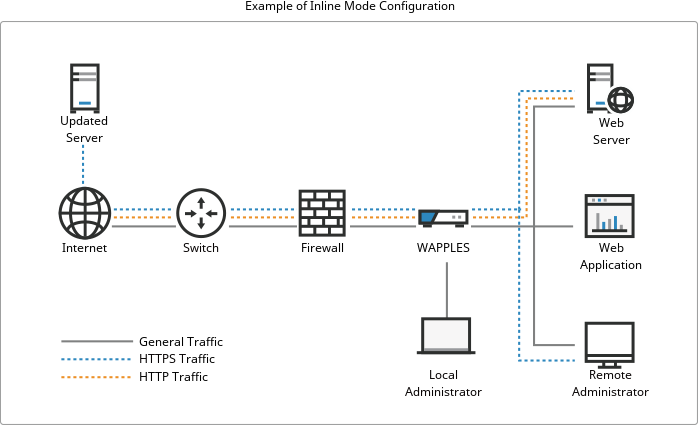
Deployment
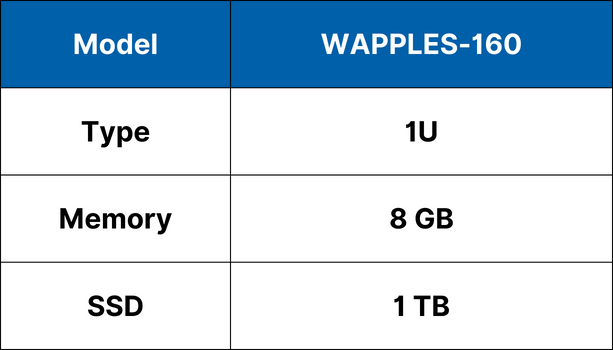
Specifications
Economy
Value
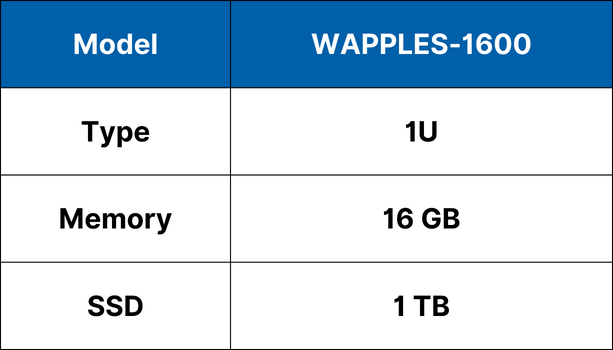
Performance

High-End

*Specifications subject to change without notice.
Implementation
When a customer chooses to deploy WAPPLES, a thorough analysis of the customer environment will be conducted prior to installation. This is important for optimizing policy settings tailored to specific operational and business needs to achieve an optimal configuration. Post-installation, detection logs are also monitored over a period of time and analyzed to further fine-tune the security policies and complete the implementation process.
- Pre-Inspection
- Pre-inspection
- Install and Configuration
- WAPPLES installation
- WAPPLES configuration
- Operation testing and demonstration
- Supplement Policy
- Detection log analysis
- Analysis report
- Policy modification